The security flaw in question was detected by Google and reported to Epic Games on 15 August 2018. According to the report, "this vulnerability allows an app on the device to hijack the Fortnite Installer to instead install a fake APK with any permissions that would normally require user disclosure."
Google's engies even sent proof of their claims in form of a video clip, which shows an Android phone installing Fortnite, only to be substituted by the fake APK along the way. It's actually almost scary how inconspicuously the process went along so fair play to Google.
As you'd expect Epic Games responded instantly and said they managed to replicate the bug and that they "have a team working around the clock to fix it." This Fortnite security team actually managed to tackle the bug in less than two days, reporting to Google once they've had the patch ready to go.
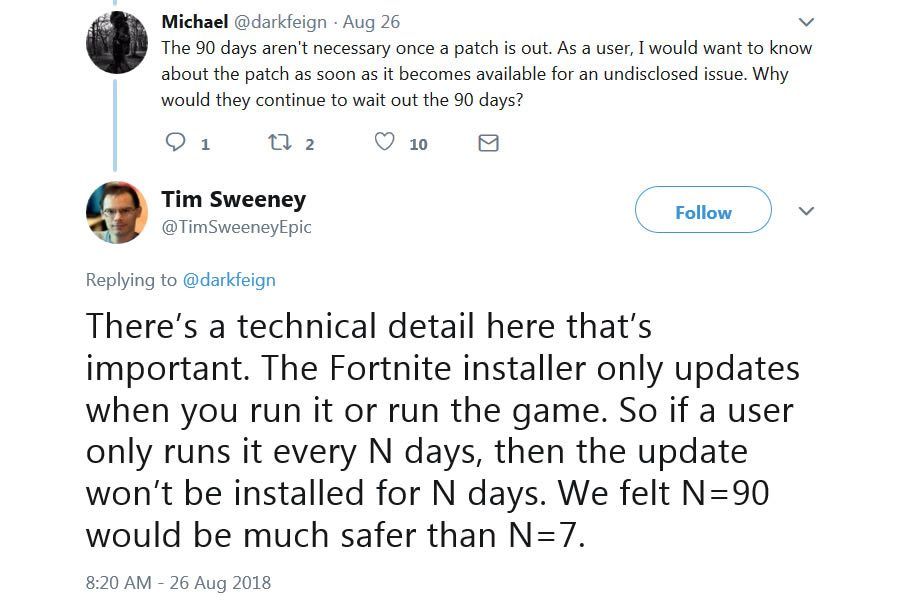
However, and there had to be a however here, Epic also asked to be given 90 days before the vulnerability is publicised, which Google refused to do. Even though 90 days is standard for these things, Google's policy for fixed flaws is to wait 7 days before making it public.
Unfortunately, this didn't sit well with Epic and the company's CEO Tim Sweeney even took to twitter to voice his displeasure of Google's move. While fully aware and respectful of Google's policy, Sweeney pointed out that if security was indeed their concern, they should've complied.
Naturally, everyone's mind immediately went to 's Play store, where Epic kindly passed the opportunity to hand over 30 per cent of Fortnite's earnings.
And I must admit - while you'd be hard pressed to find foul play in any of Google's security reports, because they've truly been invaluable to the industry, the company's refusal to comply is at least peculiar.
You can find the report in question .
Fortnite: Battle Royale, Season 5 of Epic's monster